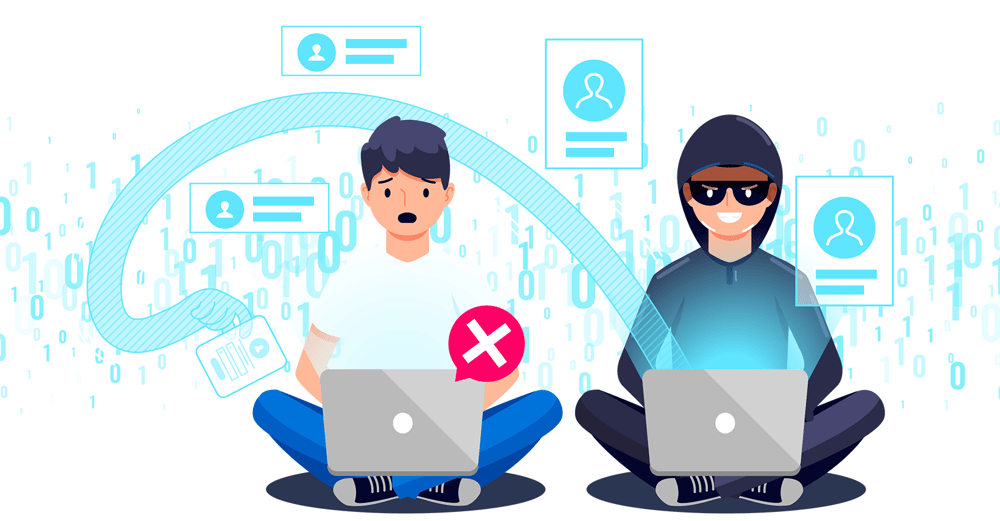
Ransomware attacks have been increasing and getting more vicious throughout the years. And as cybercriminals get more devious, cyber security professionals must be smarter to protect company data from unauthorised access and hold it for ransom.
According to McAfee, a computer security company, ransomware is a type of malware that encrypts files and allows cybercriminals to demand ransom (usually in cryptocurrencies). This attack is especially dangerous because if a company falls victim to ransomware, not only will they lose access to their data, applications, and files (unless they have a reliable backup solution in place), but there is also a massive chance for it to be stolen and used for illegal activities.
The Australian Government’s Department of Home Affairs estimated that for every 11 seconds, there will be at least one ransomware attack worldwide. They estimated that total ransomware damages may total up to US$20 billion in just 2021 alone.
No business, whether big or small, is invulnerable to ransomware attacks. Every industry is at risk of ransomware and other cyberattacks. They are growing and getting more sophisticated by the day. And usually, companies that have weak security or legacy IT systems are often their best victims.
There is no perfect way to protect your company from all kinds of ransomware attacks. One way or another, there will come a time when you’ll be exposed, and the best way to protect yourself is to devise cyber security policies with a deep understanding of the impacts of cyber risks, especially ransomware attacks.
If and when your company gets hit by a ransomware attack, there are specific cyber security measures you can take to protect your data and mitigate damages as much as you can.
What to do when hit with a ransomware attack
Disconnect all infected devices from your networks
Any computer virus always has a source. The challenge is to find that infected device (and all the other devices it has infected) to disconnect them at once from your networks. This is an essential process to prevent the malware from spreading through your entire system, causing more IT headaches.
If there happens to be more than one infected device, there’s a chance that the malware may have infiltrated through multiple devices or has remained undetected in your systems and just waiting to attack. That’s why you can never be too sure that all devices you find are the only ones infected. You must always take the necessary security measures to ensure your systems are unaffected by the ransomware attack.
If several of your systems are infected, you will need to switch your networks offline to prevent more damage rather than disconnecting infected systems individually. But if that’s not possible, you will need to find the network cable(s) the infected devices are connected to or disconnect them from the internet to localise the problem.
Identify the ransomware
The purpose of identifying the ransomware that attacked your system is to understand how it operates, infects different devices, and what you can do to remove it from your network. Doing so will enable you to create the necessary action plan that will help prevent the malware from spreading to other devices and throughout your network.
When ransomware attacks your system, it usually identifies itself in its ransom message. But if it was not mentioned or you want to double-check, several trusted websites can help you, such as NO MORE RANSOM, ID Ransomware, and Varonis.
Reformat the infected device
The best way to remove any malware from your system is to reformat all the infected devices. This process ensures that no traces of malware remain on your system, and you can reinstall your OS and other applications safely.
If your company has a backup strategy, complete data restoration is possible to bring back your device to the way it used to be before the infection.
Always double-check if everything doesn’t have any remaining malware
Think of that one guy who hides bite marks in zombie movies. You wouldn’t know that you have an infected person in your group until it’s too late.
The same goes for computers if you don’t verify that it’s free from all types of malware before you retrieve your backup.
Once you’ve reformatted your device, always verify and double-check for any remaining malware. It is also best to check if your backup and the network you’re connecting to are free from any visible or hidden infections. This process will prevent unseen ransomware attacks from infiltrating your newly reformatted device, rendering your efforts useless.
Restore devices into a clean network with all the necessary applications
This step is where having a backup solution plays an important role. If your company has reliable cloud backup, you can retrieve your files anytime and get your operations up and running in no time (once you’ve verified that there’s no remaining malware in your local computers).
You will also have to reinstall your operating system and office applications and update them to their latest versions to tighten up your cyber security even further for fewer chances of a ransomware attack.
Once you’ve restored everything to its former glory, you will need to implement the use of stronger and more unique passwords throughout your company – especially those with executive access. Password managers are amazing tools for keeping all your account credentials and other important information safe without the need to remember each one of them. You only need to remember the username and password for your password manager to access these on your computer or mobile device.
Reset administrator and system account credentials
Human error is still the number one cause of triumphant ransomware attacks because company staff use weak and/or predictable passwords. Seeing passwords like “123456789” and “qwerty” brings nothing less than disappointment.
Companies need to impose password policies on their employees, especially executives and directors. Consider these rules in the password clause of your cyber security policy:
- Passwords must have at least ten characters
- Ese a combination of numbers, uppercase and lowercase letters, and symbols
- Establish 2-factor Authentication on all your accounts
- Never use the same password on different user accounts
A company-mandated cyber security education is still the best defence against these risks that can otherwise damage business operations and profits. Security awareness training should be taken every six months and updated over time.
What you can do in the future to protect your business against ransomware attacks
As ransomware attacks are growing every year, it’s our responsibility to protect our data in various ways to lessen the chance of a breach.
If you were a victim of a malware attack, evaluate how the attack took place, how it spread through your network or on multiple devices (if it did), and what you could do to prevent it in the future.
According to the Australian Government’s Ransomware Action Plan, “Strengthened response mechanisms for ransomware victims will help protect Australia and reduce the incentive to pay ransom.” Paying a ransom should never be an option, as this only opens you to several dangers, such as:
- Unguaranteed system outcomes
- Encourage cybercriminals to do more ransomware attacks in the future.
- Release or sell your confidential data to other cybercriminals
The best way to prevent ransomware attacks from infiltrating your IT is to implement consistent security awareness training for your employees and establish reliable security and backup solutions. These should go hand in hand in protecting your information and preventing any expensive business downtime.
Did you know that right at this moment, you might be at risk of ransomware attacks?
If someone decides to launch a full ransomware attack on your business, will your IT security handle the load? Does your staff have sufficient security awareness training?
Sign up for a complimentary IT Health Check here to defend your business against nasty ransomware attacks.
We’ll personally look for any security vulnerabilities in your IT and evaluate the areas that need attention. As a bonus, we’ll also provide a business IT risk assessment to bulletproof your data.