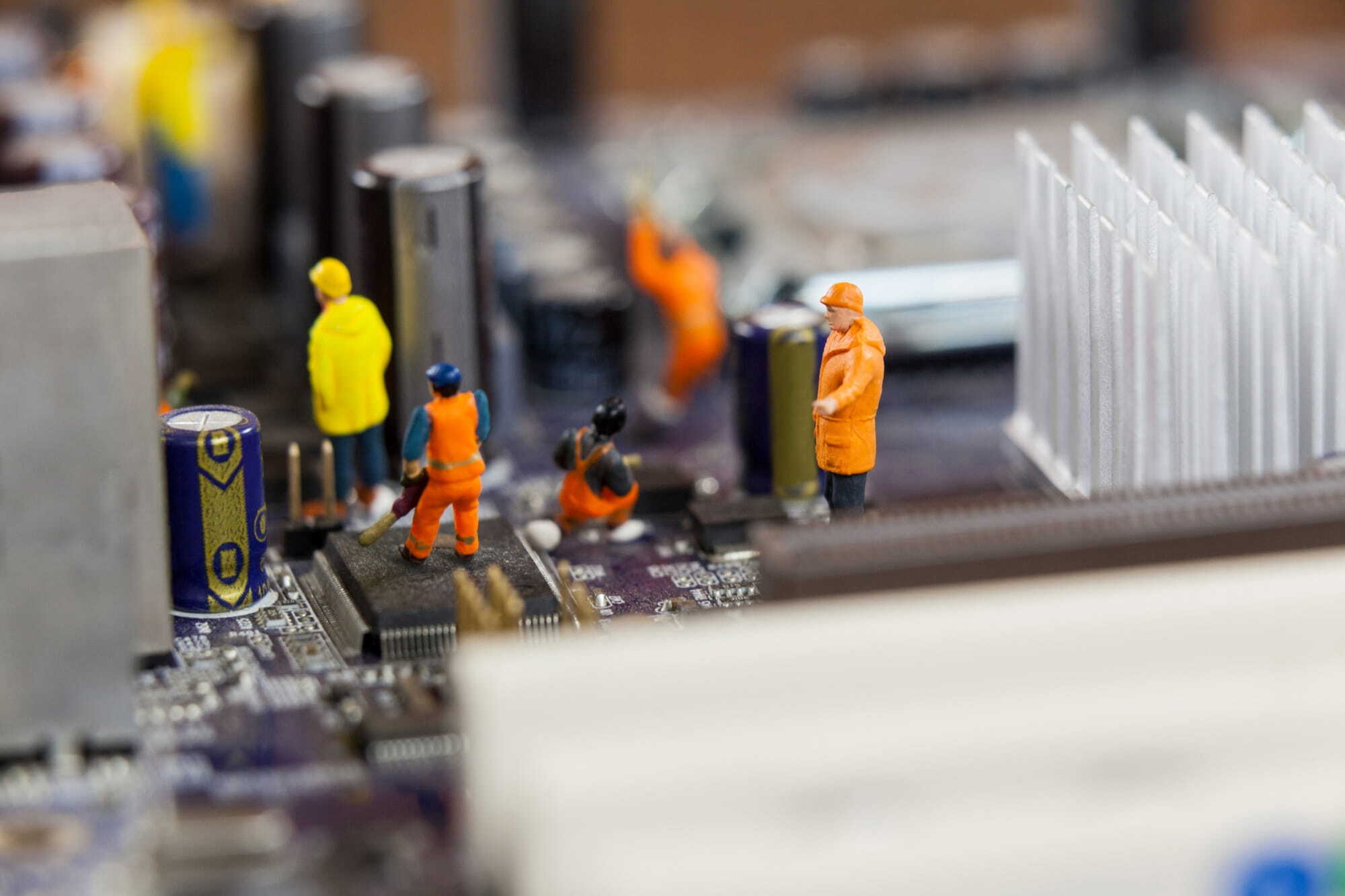
The business world today is tough. You must fight not only against competitors for sales but also against cybercriminals to secure confidential information in your business.
Your data is a business asset. Since it is a critical component in business success and continuity, it is only fair to protect it from exploitation. And one way to do that is to establish a cyber security solution that can help you withstand internal and external attacks.
Data can range from customer and employee data to sales and marketing strategies. You need to manage and protect it appropriately to reduce the risk of a security breach that will lead to complications such as lawsuits, reputation damage, and profit loss.
Cyber security is a critical business component, typically if you’re relying on technology to operate smoothly. The more you prioritise security, the more you’re keeping your confidential business information secured from cyber disasters. Luckily, there are ways to do that.
Below, we will share the ten best ways to secure confidential information in your business.

How to Protect Confidential Information
1. Do a data inventory
The first step in implementing an IT project to keep office information confidential is to have an accurate inventory of your assets so you know what you need to protect.
Creating a comprehensive inventory of the data assets in your business will help you know:
- where your data is coming from
- the type of data you collect
- where it is stored
- the people who have access to it
- how your staff uses it
- which data to prioritise
Performing data inventory (or data mapping) goes all around your business. Consider all departments that contain and work with data. This process will give you insights into the status of your overall data and help you decide on the best options for protecting it.
Keep in mind that every business process is unique. So your data inventory approach may differ from the standard guideline.
Start taking notes of what you want to achieve in your data inventory, then start building from there.
If this process is too much work, you can always reach out to a managed IT service provider known for conducting data inventories. This way, you'll see where your data stands in terms of organisation, usage, and security.
2. Only keep what you need
As much as you would like to store all the data that comes into your business forever, it’s just not technologically possible for a couple of reasons.
First, it will become a liability in your data storage. The bigger the data you store, the higher your data storage costs and the harder it is to manage. The key to making the most out of our data storage is to keep the essential ones. Then digitally shred the ones you don’t.
Second, you’ll end up violating data privacy laws by keeping it longer than necessary. The key is always to consider compliance policies when retaining customer data. First, note the required minimum retention periods and other requirements.
The key to keeping your business information safe is to only manage the data you need. Data hoarding is never a good idea.
3. Only use private networks
Ever since there was a sudden increase in remote work setups, cyberattacks have increased along with it.
Businesses had little to no control over the networks their employees were connected to, since they could either be working on their home network or in a coffee shop. This situation is dangerous to your security since bad actors connected to the same network can monitor your online activity.
So to keep confidential information safe, you need to implement VPNs to hide your identity and encrypt your connection if you're using a shared public network.
If a VPN is not available, you can opt for a password-protected personal hotspot instead to reduce the risk of hackers looking into your activity, especially if you’re working on a confidential file.
4. Conduct security awareness training for your employees
Your employees are usually the weakest link in securing confidential information in your business.
According to SentryBay, 95% of cyber security breaches are from human error.
One of the best ways to prevent being a part of that statistic and effectively protect confidential information is to conduct bi-annual security awareness training for your employees. This way, they’re aware of what to do and what to look out for.
5. Implement control access
A business that limits access to its confidential information has a higher chance of reducing its risk of a data breach than those that don’t.
To maintain the security and confidentiality of your business data, only share it with employees on a “need to know” basis. This access control protocol applies to hard and soft copies of documents.
Keep hard copies in a locked safe and put password protection on soft copies.
File encryption can also be an option if you store files on a removable hard drive.
6. Encrypt stored data
Encryption is your best friend when it comes to maintaining information confidentiality.
It works by adding another layer of security to a file to protect it from unauthorised access. Businesses that encrypt sensitive files before sending them have one less cyber security problem to worry about.
But don’t just stop there.
To secure confidential documents, you should also encrypt files, especially restricted ones - even if they’re only sitting in your storage network. Implement this security policy with your staff and ensure they’re comfortable with this process.
7. Encrypt files before sending them
File encryption is your best friend when sending confidential files online. This trick helps keep your files secure, especially if an unauthorised entity intercepts your email. You should also only use trusted service providers when sharing your emails, but ensure that they are encrypted beforehand.
It’s the same thing when dealing with physical confidential files. Only use courier services you trust to protect your confidential information.
Better yet, get someone from your organisation to deliver it themselves to ensure its safety.
8. Shred outdated data
Paperwork still plays a crucial role in a business's day-to-day operations in the digital era.
Usually, when businesses need to dispose of the hard copies of their confidential data, they run it through the shredder or chuck it in a classified trash bin. But deleting digital copies for good is a lot more complicated than that.
We recently did an article about whether your files are gone for good after you delete them from the Recycle Bin.
And the short answer is no.
Your files are not gone after permanently deleting them from the Recycle Bin.
A copy of it is still on your hard drive and still very much accessible by someone with high-level tech skills.
One way to prevent that from happening is to digitally shred your files or use a third-party application that will overwrite your hard drive with random data to replace the old files stored there.

9. Implement a cyber security policy
A business without a cyber security policy is one step away from a digital disaster.
When you’re handling sensitive data such as customer information and inventory records, you should have clear guidelines about how to handle them and keep them secure.
A cyber security policy plays an integral role now more than ever, since more employees prefer to work remotely than in the office. If implemented successfully, your team will be more efficient in keeping confidential information secure wherever it is.
Your cyber security policy should coincide with how your business operates.
Be specific about the security measures in your policy. For instance, only using strong (unique, long, and complex) passwords for corporate accounts and enabling two-factor authentication.
Refer to this cyber security policy template to learn more about what you should and shouldn't include in your policy.
10. Be religious with your backup
Backing up your data will protect your business if you fall victim to a cyberattack like ransomware.
When you no longer have access to your data, your business comes to a standstill. This problem can result in profit loss, reputation damage, and even business closure.
To prevent that, always keep physical and cloud backups of your data that you can access anytime in case of an emergency. But to fully appreciate this solution, you must keep your backups up to date.
Optimise the Way You Protect Your Confidential Information
There are plenty of ways to protect confidential information from cyber threats and risks. The more you put the security practice within your organisation, the more secure you'll be.
When setting up your cyber security, be sure to customise it to fit your specific needs and industry for the best protection.
With a cyber security service provider by your side, you can strengthen your defences and carry on with your business confidently, knowing your assets are well-guarded. If you need further help with establishing a strong cyber security solution for your business, your friendly neighbourhood IT security & support guys are willing to help.
Frequently Asked Questions
How can you protect confidential data and information?
Encryption is a great way to protect your confidential data and keep it safe and sound. When your data is encrypted, it gets transformed into a format that’s unreadable to anyone without permission. Even if someone manages to access or steal your data, they won’t be able to make sense of it without the decryption key. So, rest easy knowing your files are still secure!
How do I keep my information confidential?
Besides encryption, there are some other friendly ways to protect confidential information. For instance, you can wipe hard drives clean before selling or retiring devices, and make sure to delete backup and original files from all your storage spots, like the cloud, local servers, and hard drives.
If you’re dealing with paper documents, don’t forget to remove important details like names, birthdates, addresses, and financial info (if you have them) before shredding and tossing them out.
How can we prevent confidential information leakage?
Aside from preventing cyber threats from infiltrating your IT, it's also important to focus on stopping any leaks of confidential information. Luckily, there are some friendly ways to tackle this within your organisation.
First, it's a great idea to boost security awareness among your team, especially when dealing with sensitive customer info. You can host regular training sessions on security practices and ways to handle potential insider threats.
Second, if you're dealing with sensitive documents, make sure to dispose of them properly—either by shredding paper documents or securely destroying storage devices, especially if they're outdated or no longer in use.
Lastly, consider setting up security classification redundancy systems to enhance data security based on their sensitivity, adding multiple layers of protection for those crucial pieces of information.








.jpg)